In November 2023, Boeing’s parts and distribution business disclosed that a LockBit ransomware affiliate had exfiltrated roughly 43 gigabytes of internal data.
The entry vector was not a zero-day. It was a Citrix NetScaler appliance that had gone 47 days past a published patch. Boeing’s internal post-incident review, later summarized by the Cybersecurity and Infrastructure Security Agency, found that the affected appliance had never been included in the quarterly IT risk inventory.
A single asset omission in a computer system risk assessment cost a Fortune 100 manufacturer tens of millions of dollars and months of regulatory scrutiny.
| Key Takeaways: Computer System Risk Assessment |
| A computer system risk assessment identifies information assets, maps threats and vulnerabilities against them, scores residual risk, and selects controls. Done properly, it converts fear into a prioritized work list. |
| The three dominant standards are NIST SP 800-30 Rev 1 for US federal and general use, ISO/IEC 27005:2022 for international and commercial organizations, and GAMP 5 Second Edition for regulated life sciences. |
| IBM’s 2025 Cost of a Data Breach Report puts the global average cost per breach at 5.17 million dollars. Organizations that completed a computer system risk assessment within the prior 12 months saved on average 1.6 million dollars per incident. |
| A computer system risk assessment is not a one-time exercise. NIST, ISO, and the FDA’s 2024 Computer Software Assurance guidance all require continuous monitoring with triggered reassessment on system change, incident, or regulatory update. |
| The most common failure mode is treating the computer system risk assessment as a compliance document. If the output is not a prioritized control backlog owned by named individuals, the assessment has failed. |
| AI systems, third-party SaaS, and cloud workloads have pushed the scope of computer system risk assessment far beyond on-premise servers. Modern assessments cover data flows, model risk, and supply chain exposure. |
That is the stakes of getting a computer system risk assessment right. It is not paperwork. It is the scaffolding that decides which of your systems gets patched on Tuesday and which waits until next quarter.
This guide walks through the frameworks that matter (NIST SP 800-30, ISO/IEC 27005, GAMP 5), the step-by-step process, sector-specific requirements for regulated industries, and the pitfalls that turn a good computer system risk assessment into shelfware.
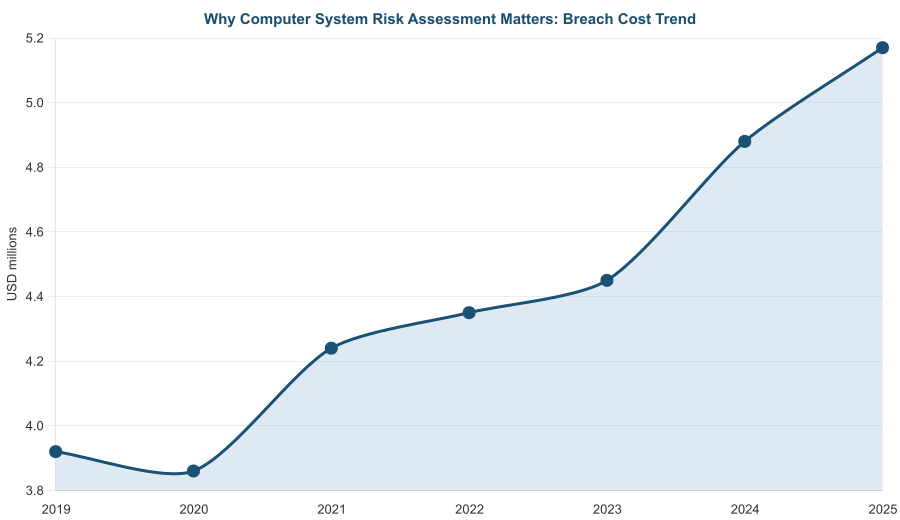
Figure 1. Why a computer system risk assessment matters: global average breach cost trend, 2019-2025. Source: IBM Cost of a Data Breach Report 2025.
What a Computer System Risk Assessment Actually Does
A computer system risk assessment is the structured process of identifying information assets, mapping threats and vulnerabilities against those assets, scoring the resulting residual risk, and selecting controls.
It sits at the core of any IT risk management program and feeds directly into the organization’s risk register and risk heat map.
The canonical formula, drawn from NIST SP 800-30 Rev 1, expresses residual risk as a function of threat likelihood, vulnerability, and asset impact.
A threat that cannot exploit any vulnerability is not a risk. A vulnerability that exposes no valuable asset is not a risk either. The assessment forces you to map all three dimensions simultaneously, which is harder than it sounds when assets, threats, and vulnerabilities all change weekly.
Why a Computer System Risk Assessment Pays For Itself
The IBM 2025 Cost of a Data Breach Report puts the global average cost per breach at 5.17 million dollars, up from 3.92 million in 2019. More importantly, organizations that completed a documented risk assessment within the 12 months before an incident saved on average 1.6 million dollars per breach through faster containment.
That number alone justifies the three to eight weeks of effort a full computer system risk assessment typically takes.
Regulatory drivers have also sharpened. The SEC’s 2023 cybersecurity disclosure rule now requires public companies to disclose material cyber incidents within four business days and report on their risk management processes annually.
The European NIS2 Directive imposes similar requirements. Without a current computer system risk assessment, meeting these disclosure obligations is guesswork.
The Computer System Risk Assessment Frameworks That Matter
Three frameworks dominate the computer system risk assessment landscape. They are compatible rather than competing: mature organizations use one as the primary reference and map the others as overlays.
| Framework | Best for | Strengths | Known gaps |
| NIST SP 800-30 Rev 1 | US federal, defense, general IT | Prescriptive, widely adopted, maps cleanly to NIST CSF 2.0 | Lighter on supply chain and model risk |
| ISO/IEC 27005:2022 | Commercial, international, financial services | Process-oriented, aligned to ISO 27001 ISMS, strong on governance | Less prescriptive on threat catalogs |
| GAMP 5 Second Edition (2022) | Life sciences, GxP-regulated, pharma, medical device | Risk-based validation, aligned with FDA Computer Software Assurance | Narrowly scoped to regulated-industry systems |
| NIST CSF 2.0 (2024) | Mid-market and enterprise cross-industry | Clear five-function model, executive-friendly | Not a pure risk-assessment standard; refers out to SP 800-30 |
| FAIR (Factor Analysis of Information Risk) | Quantitative risk programs, mature shops | Monetizes risk in dollar terms for boards | Data-hungry, requires quantitative discipline |
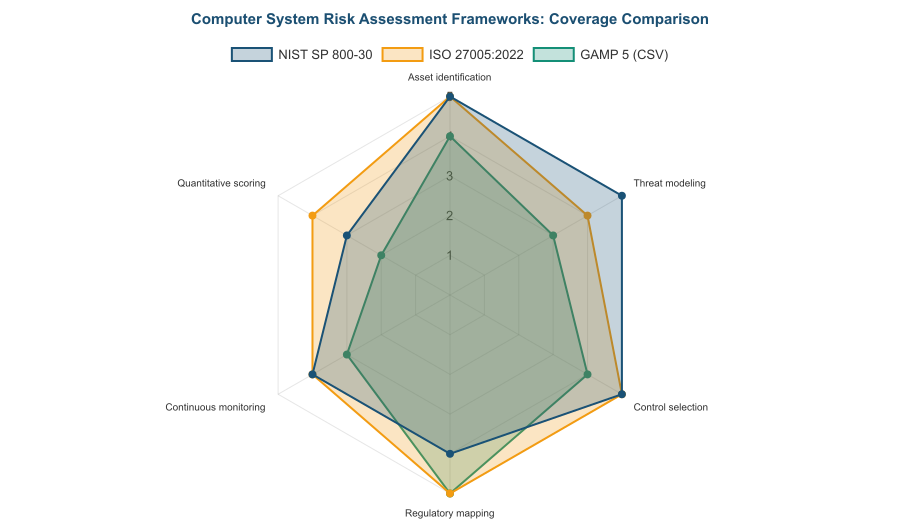
Figure 2. Computer system risk assessment frameworks compared on six capabilities. NIST SP 800-30 leads on threat modeling; ISO 27005 on continuous monitoring and quantitative scoring.
Mapping the Frameworks in a Single Computer System Risk Assessment
A common pattern in regulated industries is to run the ISO 27005 process as the engine, mapped against ISO/IEC 27001:2022 Annex A controls for control selection, with NIST SP 800-30 threat catalogs feeding threat identification, and GAMP 5 categories driving the validation depth for GxP systems. None of these should be treated as optional.
The FDA Computer Software Assurance guidance finalized in 2024 explicitly calls for a risk-based approach that echoes GAMP 5 principles.
The 7-Step Computer System Risk Assessment Process
The steps below work across frameworks. The vocabulary varies, but the sequence does not.
Step 1: Define Scope for the Computer System Risk Assessment
Scope is where most computer system risk assessments fail before they begin. Either the scope is too broad (every system in the enterprise) and the assessment never finishes, or too narrow (one application) and the results are not useful for prioritization.
A good scope statement names the business processes, the supporting systems, the data classifications, the external interfaces, and the exclusions. Document the scope formally in your risk assessment policy.
Step 2: Inventory Assets in Your Computer System Risk Assessment
The asset inventory is the foundation. If an asset is not on the list, it will not receive controls. List hardware, software (including shadow IT), data stores, network segments, people with privileged access, and critical third parties. For each asset, capture owner, business process served, data classification, and recovery priority tier.
Many organizations discover during Step 2 that they have no single source of truth for assets. A configuration management database (CMDB) is the usual anchor, supplemented by cloud account discovery and software-bill-of-materials tools.
Align this asset register with your business continuity impact analysis so that recovery priority tiers are consistent across programs.
Step 3: Identify Threats and Vulnerabilities in the Computer System Risk Assessment
Threat identification uses a combination of reference catalogs and internal data. The MITRE ATT&CK framework is the current gold standard for tactics, techniques, and procedures. The Verizon Data Breach Investigations Report provides empirical breach patterns by industry.
The ENISA Threat Landscape adds European and geopolitical context. Vulnerabilities come from scanner output, penetration test findings, audit reports, and incident history.
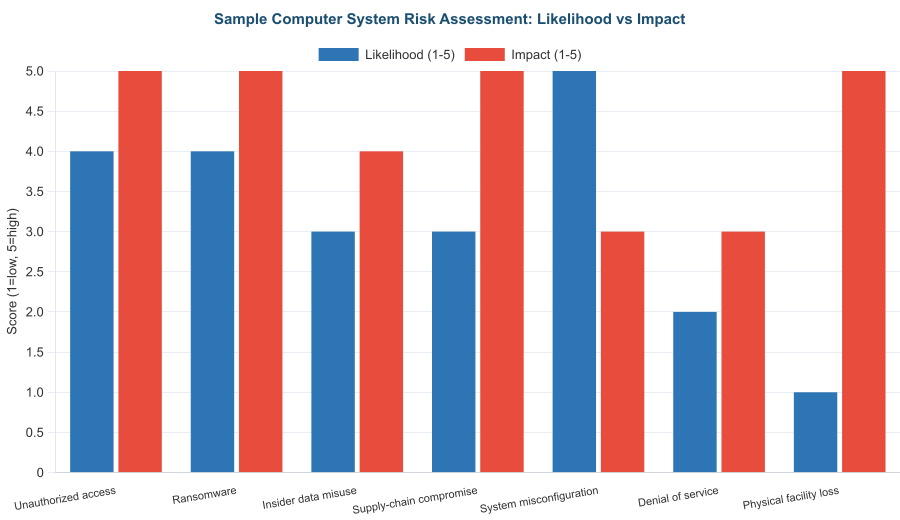
Figure 3. Computer system risk assessment: breach source distribution from the 2025 Verizon DBIR. External actors still dominate, but phishing and misconfiguration together account for 38 percent.
Step 4: Analyze Likelihood and Impact in Your Computer System Risk Assessment
For each asset-threat-vulnerability triplet, assign likelihood and impact scores. Qualitative 1-to-5 scales are the most common approach. Quantitative approaches using the FAIR model produce dollar-denominated loss estimates that resonate with boards.
Impact should reflect confidentiality, integrity, and availability damage, mapped against your organization’s risk appetite statement.
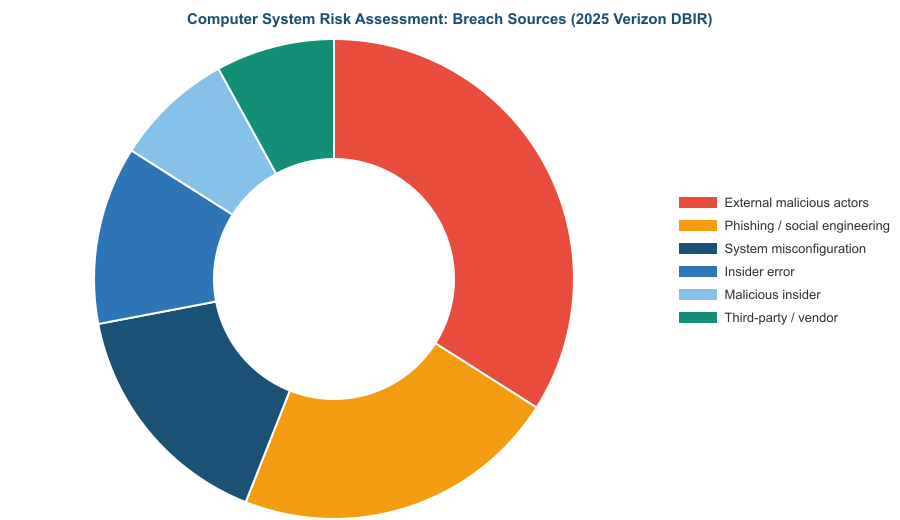
Figure 4. Sample computer system risk assessment output: seven risks scored for likelihood and impact. Ransomware and unauthorized access top the list because both scores are high.
Step 5: Evaluate Controls Against the Computer System Risk Assessment Findings
For every high and medium risk, map existing controls and judge their effectiveness. Use the CIS Critical Security Controls v8.1, NIST SP 800-53 Rev 5, or ISO 27001 Annex A as your control reference.
Rate each control as not implemented, partially implemented, implemented, or optimized. The gap between current control state and target state becomes the control backlog.
Step 6: Treat and Document in Your Computer System Risk Assessment
Choose a treatment for every risk: mitigate, transfer, avoid, or accept. Assign a named owner, a target completion date, and a success criterion. Feed the outputs into the risk register and link to risk mitigation strategies in your broader ERM program.
Step 7: Monitor, Review, and Iterate Your Computer System Risk Assessment
The computer system risk assessment is a living artifact. Review it at least annually. Trigger unscheduled reviews on major system changes, significant incidents, regulatory updates, or third-party events. Wire key risk indicators into each domain so that drift is visible between formal reviews.
Computer System Risk Assessment for Regulated Industries
Financial services, healthcare, and life sciences face layered requirements that extend the baseline computer system risk assessment with sector-specific validation and disclosure obligations.
Computer System Risk Assessment Under FDA CSV and CSA
For pharmaceutical, biotech, and medical device manufacturers, computer system validation (CSV) and the newer Computer Software Assurance (CSA) approach shape the risk assessment. The FDA 21 CFR Part 11 rules on electronic records and signatures remain the anchor regulation.
The 2024 FDA CSA guidance shifts emphasis from exhaustive documentation to risk-based assurance effort, which means a sharper computer system risk assessment carries more weight than it did a decade ago.
Computer System Risk Assessment Under GAMP 5
GAMP 5 Second Edition, published by ISPE in 2022, categorizes computerized systems from Category 1 (infrastructure) to Category 5 (custom applications).
The risk assessment determines the validation rigor. A Category 5 clinical trial management system demands deep specification-based testing. A Category 3 commercial off-the-shelf tool used in a non-GxP context may need only supplier assessment and configuration verification.
Computer System Risk Assessment for Financial Services
US banks follow FFIEC IT Examination Handbook guidance, which requires documented risk assessments covering information security, business continuity, and third-party management.
The Federal Reserve SR 11-7 model risk management guidance extends the computer system risk assessment to any model that drives financial decisions. The current wave of AI adoption means model risk now sits squarely inside the computer system risk assessment scope.
Computer System Risk Assessment and Third-Party Risk
Third-party and supply-chain exposure has exploded. The 2025 Verizon DBIR attributes 8 percent of breaches to vendor entry points, but post-Boeing and SolarWinds, the effective blast radius is far larger.
Your computer system risk assessment should integrate with third-party risk management and compliance risk assessment workflows so that vendor posture is continuously reassessed.
Scoring Risks in a Computer System Risk Assessment
Most organizations use a qualitative 5×5 risk matrix. The simplicity is the point. Quantitative methods add precision but require data many organizations do not have. Our risk assessment methodology covers the scoring options in depth.
| Likelihood \ Impact | Negligible (1) | Minor (2) | Moderate (3) | Major (4) | Catastrophic (5) |
| Rare (1) | Low | Low | Low | Medium | Medium |
| Unlikely (2) | Low | Low | Medium | Medium | High |
| Possible (3) | Low | Medium | Medium | High | High |
| Likely (4) | Medium | Medium | High | High | Critical |
| Almost certain (5) | Medium | High | High | Critical | Critical |
Critical risks demand immediate treatment. High risks need a treatment plan with a board-visible completion date. Medium risks enter the backlog.
Low risks are monitored. The bands should match the organization’s risk appetite, not a generic template. This scoring feeds directly into enterprise risk management dashboards.
Common Pitfalls in Computer System Risk Assessment
| Pitfall | Why it happens | How to fix it |
| Asset inventory is incomplete | Shadow IT, cloud sprawl, and SaaS subscriptions escape central IT oversight | Combine CMDB, cloud discovery, and SaaS management tools; treat unknown assets as critical-priority |
| Threats are generic, not specific | Teams copy a boilerplate threat list from a template | Anchor threat identification in Verizon DBIR industry data and MITRE ATT&CK techniques relevant to your stack |
| Scoring is subjective and inconsistent | No calibration exercise; different analysts assign different scores to identical risks | Run a calibration workshop; document scoring rubrics with examples for each score level |
| Controls are assumed, not tested | Control existence is confirmed on paper but not verified in practice | Pair every high-risk control with a testing method: scan results, penetration test, audit trail review |
| Outputs have no owner | Risks are documented but not assigned | Require a named human owner and review date for every risk above low |
| Third-party systems are excluded | Scope is limited to internally-managed systems | Include all third-party SaaS and vendor-hosted platforms that process regulated or business-critical data |
| Assessment is run once and filed | Risk assessment treated as a compliance artifact, not a living tool | Schedule annual formal reviews and event-triggered reassessments; automate KRI monitoring between reviews |
Frequently Asked Questions About Computer System Risk Assessment
How Often Should a Computer System Risk Assessment Be Conducted?
Formal assessment at least annually. Event-triggered reassessment whenever a major system changes, a significant incident occurs, a new regulation applies, or a critical vendor is added or changed.
In FDA-regulated environments, any change that affects GxP data integrity triggers a reassessment before the change goes live.
Who Should Run the Computer System Risk Assessment?
A cross-functional team. Typical composition: an information security lead as facilitator, the system owner, a data owner, an application architect, a business process lead, an internal audit representative, and a risk management representative.
For regulated systems, add a quality assurance representative. Single-function assessments miss too much.
What Is the Difference Between a Computer System Risk Assessment and a Cybersecurity Risk Assessment?
Computer system risk assessment is broader. It covers all risks to information systems including operational, regulatory, availability, and integrity exposures.
A cybersecurity risk assessment narrows the lens to threats targeting confidentiality and integrity through malicious actors. In mature programs, the cybersecurity risk assessment is a subset of the broader computer system risk assessment.
Does the Computer System Risk Assessment Cover Cloud and SaaS?
Yes. Any system that processes business-critical or regulated data is in scope regardless of where it runs. Cloud-hosted systems add shared-responsibility-model considerations: the provider is responsible for some controls, the customer for others. The assessment must map this split explicitly to avoid gaps.
How Does AI Affect the Computer System Risk Assessment?
AI adoption has expanded the scope. The NIST AI Risk Management Framework provides a companion framework that integrates with SP 800-30.
Model risk, training data risk, prompt injection, and output reliability are now first-class items in a computer system risk assessment for any system that incorporates AI decision support.
What Evidence Should a Computer System Risk Assessment Produce?
Five deliverables at minimum: a scope statement, an asset register, a scored risk register, a control gap analysis, and a treatment plan with owners and dates.
Regulated industries add validation summary reports and change-control documentation. The test is whether an auditor could reconstruct the assessment’s logic from the documentation alone.
How Long Does a Computer System Risk Assessment Take?
For a mid-sized organization covering 40 to 80 critical systems, three to eight weeks for a thorough first pass and two to three weeks for subsequent annual refreshes.
Event-triggered reassessments are faster, typically one to two weeks. Skipping steps to save time is the root of most assessment failures we see in post-incident reviews.
What Is the ROI of a Computer System Risk Assessment?
IBM’s 2025 Cost of a Data Breach Report shows organizations with a current risk assessment save an average of 1.6 million dollars per breach.
Add regulatory penalty avoidance, reduced insurance premiums, and faster deal closure with enterprise customers who require vendor risk attestation, and the program typically pays for itself within the first avoided incident.
The Future of Computer System Risk Assessment
Three forces will reshape the computer system risk assessment between 2026 and 2028. First, continuous control monitoring is replacing point-in-time assessment.
Tools that ingest telemetry from endpoints, identity systems, and cloud control planes now produce live risk scores rather than annual snapshots. The static computer system risk assessment will remain the regulatory anchor, but the operational reality is real-time.
Second, AI governance is being absorbed into the computer system risk assessment rather than living as a separate exercise.
The NIST AI RMF 1.0 and the EU AI Act require organizations to document AI-specific risks with the same rigor as traditional IT risks. Expect AI model cards, training data lineage, and output-reliability metrics to appear in 2026 assessment outputs.
Third, the SEC cybersecurity disclosure rule and European NIS2 enforcement are making the board the primary audience for the computer system risk assessment.
Executive summaries must translate technical findings into dollar-denominated business impact. Organizations that still present a computer system risk assessment as a 120-page technical report will find their boards bypassing the document entirely. The winning format in 2026 is a 5-page board pack anchored by a quantitative risk register.
The Bottom Line on Computer System Risk Assessment
A computer system risk assessment is the mechanism that turns an unbounded threat universe into a prioritized, owned work list. Without it, security investment is guesswork and regulatory disclosure is guesswork. With it, leadership can make defensible choices about which systems to harden first, which risks to accept, and which exposures to transfer to insurance or vendors.
The non-negotiables, in order of priority:
- Scope it deliberately. Business processes and data flows, not just servers and applications.
- Inventory assets ruthlessly. Shadow IT and vendor SaaS belong in scope.
- Score consistently. Calibrate the team before they score anything that matters.
- Assign named owners. A risk without an owner is an excuse.
- Iterate on triggers. Change, incident, regulation, and vendor events all demand reassessment.
The organizations that get measurable security returns treat the computer system risk assessment as a recurring operational discipline, not an annual compliance ritual. Pick the operational version.
Ready to build or refresh your computer system risk assessment? Our team helps risk and IT leaders design NIST, ISO 27005, and GAMP 5 aligned assessments that stand up to regulator and board scrutiny. Start at the riskpublishing.com services page or get in touch directly to discuss scoping for your environment.

Chris Ekai is a Risk Management expert with over 10 years of experience in the field. He has a Master’s(MSc) degree in Risk Management from University of Portsmouth and is a CPA and Finance professional. He currently works as a Content Manager at Risk Publishing, writing about Enterprise Risk Management, Business Continuity Management and Project Management.
