In February 2024, a ransomware attack on Change Healthcare disrupted prescription processing, claims, and pharmacy operations across the US healthcare system for weeks. The financial fallout topped $2.4 billion, and the operational fallout reached every pharmacy and provider that used the platform.
The incident was not unusual in 2024 — it was the high-profile version of a pattern that hit 84% of organizations globally in the past twelve months.
| Key Takeaways |
| Risk management services in 2026 fall into six categories: enterprise risk management, operational risk, cybersecurity, compliance, strategic risk advisory, and third-party risk — most organizations need depth in all six but rarely fund all six internally. |
| The global risk management consulting services market reached approximately $140 billion in 2025 and is projected to grow at 7.4% CAGR through 2030, with North America accounting for 42% of demand. |
| Cybersecurity is now the fastest-growing category of risk management services. Ransomware attacks rose roughly 49% in H1 2025, and 84% of organizations reported at least one cyberattack in the past 12 months. |
| Third-party risk management services have moved from a procurement concern to a board-level priority — newer programs now manage a median of 275 third parties, and 80% of businesses experienced supply chain disruptions in 2024. |
| A hybrid model — internal capability for daily operations, external risk management services for specialized assessments and assurance — is consistent with the IIA Three Lines Model and is the right answer for most US firms. |
| When evaluating risk management services providers, weigh framework alignment (ISO 31000, COSO ERM, NIST CSF 2.0), industry expertise, deliverable quality, knowledge transfer, and integration with your existing GRC platform. |
| Cloud-based risk management platforms held about 64% market share in 2024 and continue to consolidate. Buying the platform is rarely the hard part — operating it well is what separates leading-edge programs from the rest. |
That pattern is what risk management services exist to address. The global risk management consulting services market reached roughly $140 billion in 2025 and is forecast to grow at 7.4% CAGR through 2030.
North America accounts for 42% of global demand. The growth reflects a real shift in how organizations treat risk — from an annual checkbox exercise into a strategic capability that connects to performance, valuation, and resilience.
This guide covers what risk management services actually include, when external expertise matters more than internal capability, how to evaluate providers, and how to integrate the work with your existing frameworks.
The focus is practical — what each service does for the organization, not what a marketing brochure says it does. For an overview of the discipline itself, see the enterprise risk management framework guide on this site.
What Risk Management Services Cover
Risk management services fall into six core categories that show up on most US organizational charts and on most consulting engagement letters.
The depth and frequency of engagement varies by industry, regulatory footprint, and program maturity, but the structure below is consistent across the firms we work with. The category boundaries matter for pricing, scoping, and accountability — not just for taxonomy.
| Service Category | What It Covers | Key Deliverables |
| Enterprise Risk Management (ERM) | Organization-wide risk identification, assessment, and governance. Connects risk to strategy and performance. Aligns with ISO 31000 and COSO ERM frameworks. | ERM framework design, risk appetite statements, enterprise risk register, board-level risk reporting, risk culture assessments, maturity assessments. |
| Operational Risk Management | Risks from internal processes, people, systems, and external events — process failures, equipment breakdowns, supply chain disruptions, human error. | Operational risk assessments, control effectiveness reviews, incident management frameworks, KRI design, business process risk mapping. |
| Cybersecurity and IT Risk | Cyber threats, data breaches, system failures, privacy violations. Ransomware rose ~49% in H1 2025; 84% of organizations experienced at least one cyberattack in the past year. | Cyber risk assessments, vulnerability assessments, penetration testing, incident response planning, NIST CSF / ISO 27001 alignment, security architecture reviews. |
| Compliance and Regulatory Risk | Compliance with laws, regulations, and internal policies — SOX, HIPAA, GDPR, DORA, industry-specific obligations. Non-compliance leads to fines, penalties, and reputational damage. | Compliance risk assessments, regulatory gap analyses, compliance program design, monitoring frameworks, audit preparation, regulatory change management. |
| Strategic Risk Advisory | Risks to business strategy: market disruption, competitive threats, M&A risk, geopolitical uncertainty, technology shifts. 61% of organizations lack preparation for critical global risks. | Strategic risk assessments, scenario analysis, stress testing, competitive risk analysis, M&A due diligence risk, geopolitical risk mapping. |
| Third-Party Risk Management | Risks from vendors, suppliers, outsourcing partners, and other third parties. Supply chain disruptions, vendor security failures, contractual non-performance — 80% of businesses experienced supply-chain disruptions in 2024. | Vendor risk assessments, third-party due diligence, ongoing monitoring programs, SLA risk reviews, concentration risk analysis, vendor exit planning. |
These categories intersect more than they sit apart. A single ransomware event is simultaneously an operational incident, a cyber risk, a compliance event, a third-party exposure (most ransomware enters through a vendor), and — at sufficient scale — a strategic risk.
Effective risk management services treat the intersections as the work, not as edge cases. For how risk categories connect across the wider program, see the integrated risk management approach article.
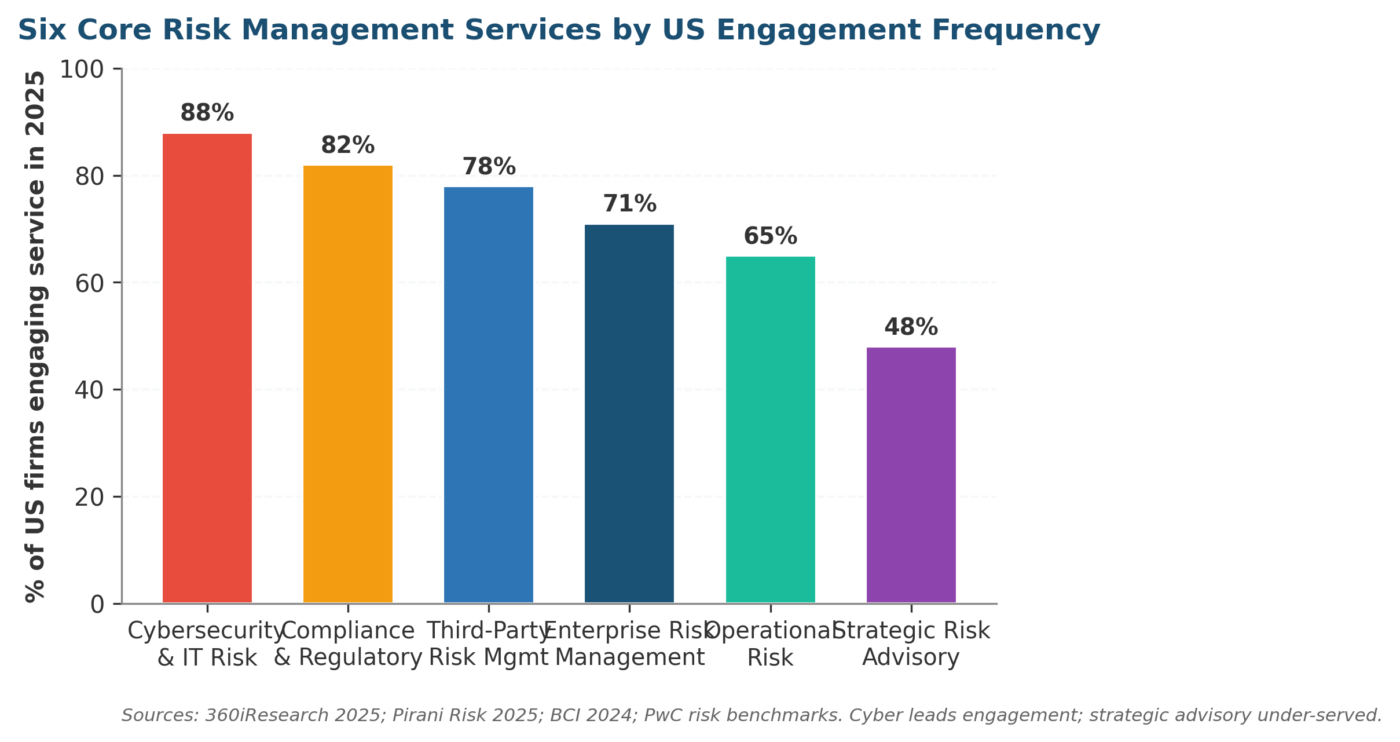
Figure 1. Six core risk management services categories by US engagement frequency. Cyber leads; strategic advisory remains under-served.
Six Core Risk Management Services in Detail
Knowing what falls inside each service line is one thing. Knowing what an engagement actually looks like in practice is where buyers usually find the gap between the proposal and the work.
The next six sections walk through what an ERM engagement does in week one versus week ten, what a typical cyber-risk deliverable contains, and where each service either earns or loses its fee.
Enterprise Risk Management Services
Enterprise risk management services build the governance, processes, and culture that hold the rest of the program together. Without this layer, individual activities — cyber assessments, compliance audits, operational reviews — operate in silos with no aggregation, no prioritization against strategy, and no clean line of sight to the board.
An ERM engagement typically opens with a maturity assessment against ISO 31000:2018 or COSO ERM.
Maturity scoring usually runs on a five-stage scale — ad hoc, initial, repeatable, managed, optimized — across governance, identification, assessment methodology, response strategies, monitoring, and reporting.
From there, the provider delivers a roadmap, framework documentation, training, and implementation support. Key outputs are risk appetite statements, an enterprise risk register, board-level KRI dashboards, and a risk-culture assessment. For framework selection, see the COSO ERM vs ISO 31000 comparison.
Operational Risk Management Services
Operational risk management services cover losses from failed internal processes, people, systems, or external events — the category most directly felt by front-line staff.
The starting point is a business-process risk assessment: walking each critical process, identifying failure modes, scoring likelihood and impact, and evaluating control design and operating effectiveness.
The output is a prioritized list of operational risks with specific control improvements. The step-by-step guide to risk assessment walks through the methodology in detail.
For organizations dependent on physical assets, complex supply chains, or critical customer-facing operations, the service line extends into business continuity management. That includes business impact analysis, business continuity planning, disaster recovery, and exercise programs.
Supply-chain risk has become the dominant operational priority — the BCI Supply Chain Resilience Report found 73% of firms now use dual-sourcing and 60% are decentralizing their supplier base.
Cybersecurity and IT Risk Management Services
Cybersecurity is the fastest-growing line within risk management services in 2026. Grand View Research recorded a roughly 49% rise in ransomware attacks in H1 2025, and global cybercrime costs are tracking past $10.5 trillion by year-end.
PwC’s 2025 risk benchmark put cybersecurity as the number-one business risk for 78% of executives — the first time a single category cleared that bar in their survey series.
Cyber risk services usually cover assessment work (vulnerability scans, penetration testing, security architecture reviews, FAIR-style quantification), framework alignment against NIST CSF 2.0, ISO 27001/27002, SOC 2, HIPAA, or PCI DSS, plus response planning and continuous monitoring through SOC services.
The line between assessment and ongoing monitoring is where buyers most often misjudge scope. For how cyber integrates with the wider program, see cybersecurity risk management.
Compliance and Regulatory Risk Management Services
Compliance services keep the organization on the right side of laws, regulations, and internal policy.
The US regulatory map alone covers SOX for public issuers, HIPAA for healthcare, the SEC cybersecurity disclosure rule for public companies, OCC heightened standards for large banks, FinCEN BSA/AML rules for financial institutions, and a thickening layer of state-level data-privacy laws that crossed thirteen active statutes by early 2026.
Typical compliance risk management services include regulatory risk assessments mapping obligations against current practice, gap analyses identifying non-compliance, program design (policies, procedures, training, monitoring), and ongoing regulatory-change management.
The financial penalty is rarely the whole story. Operational restrictions, consent decrees, and reputational damage usually outlast the fine itself, and that lag is what compliance budgets quietly underbuild against. For methodology, see the compliance risk assessment framework guide.
Strategic Risk Advisory within Risk Management Services
Strategic risk advisory addresses risks to the business model, competitive position, and long-term viability — market disruption, technology shifts, geopolitical instability, regulatory change, M&A execution, and reputational threats.
Unlike operational or compliance risks, strategic risks rarely have clean controls. They demand scenario analysis, stress testing, and strategic flexibility. PwC’s 2025 work and Accenture’s Blueprint for Success both highlight strategic risk as the most under-resourced service line.
A typical engagement combines environmental scanning, scenario analysis modelling multiple plausible futures, stress testing of the business model under adverse conditions, and risk assessments on major initiatives — new market entry, acquisitions, technology bets.
The output feeds strategic planning and board decisions, not the risk register alone. For the methodology, see scenario-based risk assessment and convergence of risk oversight with strategic planning.
Third-Party Risk Management Services
Third-party risk management services have moved from a procurement concern to a board-level priority. The BCI 2024 Supply Chain Resilience Report found 80% of businesses experienced a supply chain disruption in 2024.
Newer TPRM programs now manage a median of 275 third parties — versus roughly 80 for older programs. The risks span vendor cybersecurity failures, regulatory non-compliance by partners, reputational damage from third-party misconduct, and concentration risk.
TPRM services cover vendor risk assessment and tiering, due diligence for onboarding, ongoing performance and risk-indicator monitoring, contractual risk management (SLAs, indemnification, audit rights), and exit planning for critical dependencies.
For complex vendor ecosystems, dedicated platforms supply continuous monitoring of vendor security posture. For how third-party risks flow into the wider register, see how to manage third party risk.
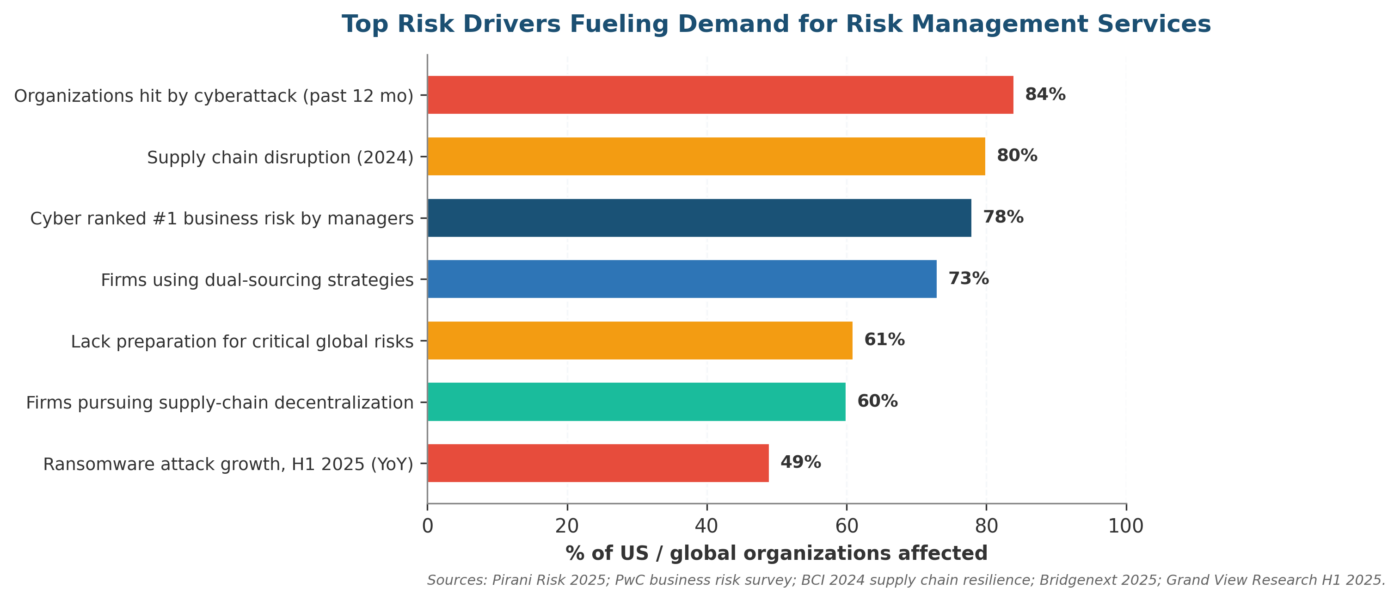
Figure 2. The risk drivers that send buyers to risk management services in 2026. Cyber and supply-chain dominate; strategic-risk preparedness lags.
Build vs Buy: When to Engage External Risk Management Services
Not every organization should outsource risk management. The right answer depends on size, maturity, regulatory intensity, and the specific skills the program needs.
The decision matrix below summarizes how we see US firms make the call across the six service lines, and where the trade-offs hide. Most organizations end up with a hybrid model rather than picking one side.
| Factor | Build Internal | Engage External Risk Management Services |
| Organization size | Large enterprises with dedicated risk, compliance, and audit teams. Sufficient scale to justify full-time specialist roles. | Mid-size organizations needing expertise but unable to justify a full risk-management department; startups scaling into regulated markets. |
| Risk maturity | Mature programs with frameworks already in place that need to operate and improve them. Internal teams maintain day-to-day operations. | Organizations building risk capability for the first time; need external expertise to design frameworks, train staff, and establish baseline practices. |
| Regulatory intensity | Highly regulated industries (financial services, healthcare) often need internal compliance teams — regulators expect embedded oversight. | External specialists for specific projects (SOX readiness, HIPAA gap analysis, GDPR implementation) and regulatory-change-monitoring services. |
| Specialization needed | Generalist coverage across the enterprise — internal teams handle day-to-day identification, assessment, and monitoring. | Specialized technical skills (penetration testing, forensic analysis, actuarial modelling, M&A due diligence) that are expensive to hire full-time. |
| Cost structure | Fixed cost — salaries, technology — with higher upfront investment but lower marginal cost per assessment over time. | Variable cost (project- or retainer-based) with lower upfront investment; scales with demand and is more efficient for periodic work. |
Most US organizations land on a hybrid model: build internal capability for daily risk operations (register maintenance, KRI monitoring, routine reporting) and engage external risk management services for periodic assessments, specialized skills, and independent assurance.
That structure aligns with the IIA Three Lines Model, where internal risk management is supplemented by external assurance. For broader process design, see five steps of the risk management process.
Technology Platforms Supporting Risk Management Services
Cloud-based risk management platforms held about 64% of market share in 2024 and adoption keeps accelerating. The platform tier you actually need depends on portfolio scale, integration depth, and whether continuous monitoring is in scope.
The three-tier breakdown below is how we see the market segmenting in 2026 — and the tier choice tends to drive the rest of the procurement conversation more than the feature checklist does.
| Platform Tier | Examples | Best For |
| Enterprise GRC platforms | ServiceNow GRC, MetricStream, Riskonnect, LogicGate, AuditBoard, Archer (RSA) | Large enterprises needing portfolio-level risk aggregation, automated workflows, multi-framework compliance, regulatory reporting, and integration across ERM, IT risk, compliance, and TPRM. |
| Cybersecurity risk platforms | SecurityScorecard, BitSight, Qualys, CrowdStrike, SentinelOne, Palo Alto Networks | Organizations prioritizing continuous cyber risk monitoring, vendor security ratings, vulnerability management, and incident response — usually integrated with the enterprise GRC platform. |
| Mid-market and specialized | LogicGate Risk Cloud, Fusion Risk Management, Pirani, NAVEX One, SAP GRC, RiskWatch | Mid-size organizations, industry-specific buyers (financial services, healthcare), business-continuity-focused programs, or buyers wanting no-code configurability without enterprise complexity. |
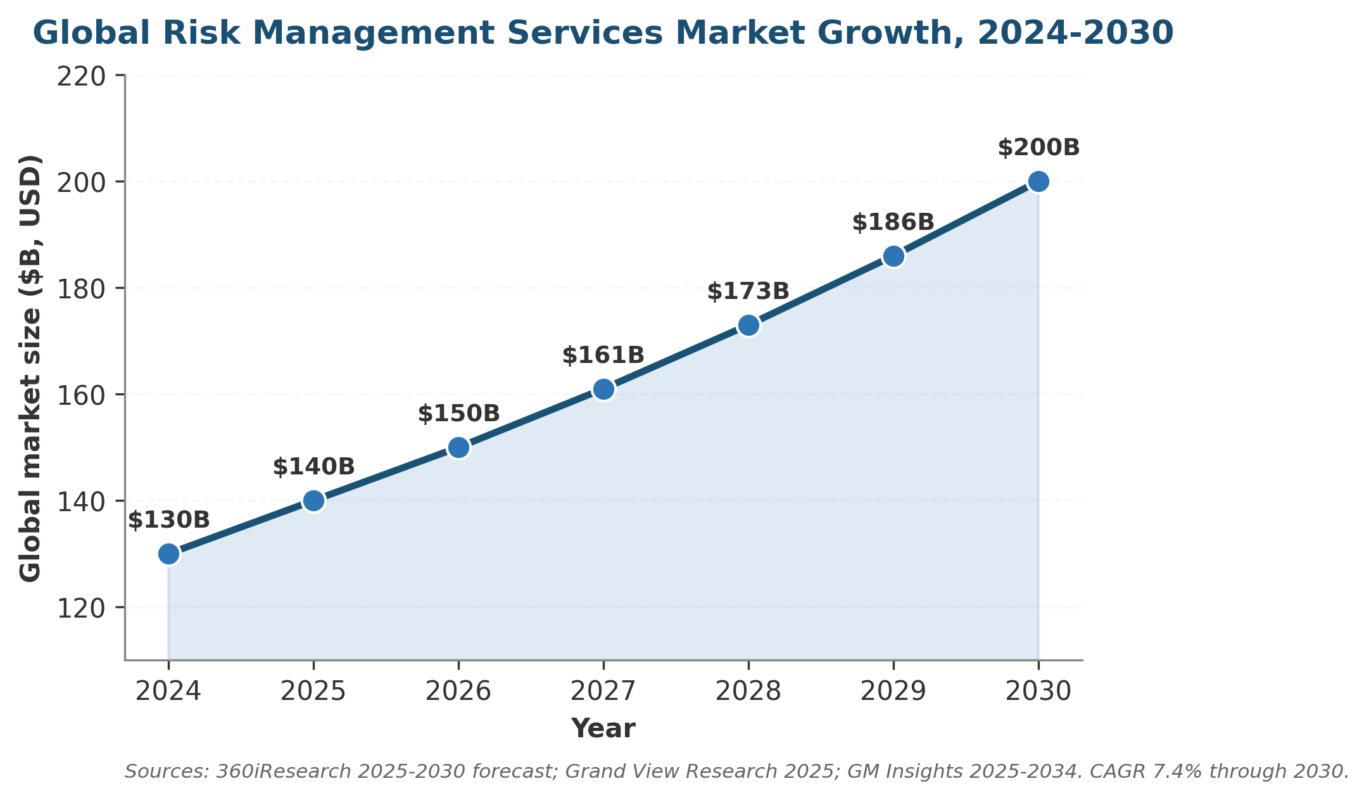
Figure 3. Global risk management consulting services market growth, 2024-2030. CAGR 7.4% per 360iResearch and Grand View Research forecasts.
Evaluating a risk management services platform comes down to fit with the operating model, not feature counts. Integration with finance, HR, and IT matters more than dashboard polish. Automated KRI collection beats manual extracts.
Multi-framework support (ISO 31000, COSO, NIST CSF 2.0, SOC 2) beats proprietary methodology that locks you in. The cheapest platform almost never wins on three-year total cost — operating discipline does.
How to Evaluate Risk Management Services Providers
If you decide to engage external risk management services, the evaluation criteria below are the ones that hold up in practice.
Each of them predicts project success more reliably than an RFP score or an analyst ranking. The list is short on purpose — most procurement failures we see came from skipping one of these checks, not from missing some exotic criterion that nobody had thought of.
| Evaluation Criterion | What to Look For |
| Industry expertise | Do they understand your regulatory environment, risk drivers, and operational context? Generic risk consultants add less value than those with deep industry knowledge. |
| Framework alignment | Do they work with recognized frameworks (ISO 31000, COSO, NIST CSF 2.0, COBIT)? Can they map their methodology to your existing standards? Proprietary-only approaches create vendor lock-in. |
| Deliverable quality | Ask for redacted sample deliverables. Are they actionable, specific, and tailored — or generic templates with your company name inserted? |
| Knowledge transfer | Does the engagement build your internal capability or does it create dependency? The best providers train your team to sustain what they build. |
| Technology integration | Can their outputs integrate with your existing GRC platform, risk register, or reporting tools? Manual handoffs between deliverables and systems waste time and create errors. |
| References and track record | Request references from organizations of similar size and industry. Ask specifically about deliverable quality, responsiveness, and whether the engagement met its stated objectives. |
Common Pitfalls When Buying Risk Management Services
Failed risk management services engagements tend to fail the same way regardless of size or industry. The traps below keep showing up in maturity reviews.
Most of them have a clean fix that costs the buyer nothing other than asking harder procurement questions before signing. The guide to risk and control self-assessment (RCSA) article describes the same pattern in the RCSA setting.
| Pitfall | Root Cause | Remedy |
| Scope creep on day one | Engagement letter is vague; consultant interprets scope to maximize hours | Lock the scope to specific frameworks, entities, and deliverables before signing |
| Generic-template deliverables | Provider re-uses prior client work with light customization | Demand redacted samples in evaluation; require explicit tailoring milestones |
| Risk register without owners | Risks logged but no first-line accountability assigned | Every risk gets a named owner and a remediation due date before sign-off |
| Cyber treated as standalone | Cyber-risk services run separately from the wider program | Wire cyber KRIs into the enterprise risk register and board reporting from day one |
| Static, annual cadence | Risk assessments run once a year and shelved | Quarterly delta review for high-severity risks; weekly automated alerts on cyber and compliance |
| Knowledge stays with the consultant | No internal training or hand-off plan | Build training and shadow-running into the engagement letter; require deliverables in editable format |
| Platform without operating model | Tool purchased before workflow is designed | Define the operating model first, then pick the platform that supports it |
Frequently Asked Questions About Risk Management Services
What are risk management services and what do they include?
Risk management services are advisory, assessment, technology, and assurance offerings that help organizations identify, assess, and manage risk across their operations.
They include enterprise risk management, operational, cybersecurity, compliance, strategic, and third-party risk lines.
Most US firms engage some combination of all six. The right mix depends on regulatory footprint, program maturity, and the specific risks the organization is exposed to. The ISO 31000:2018 standard defines the underlying methodology.
How much do risk management services cost in 2026?
Risk management services pricing ranges widely. A targeted compliance gap analysis runs $25K-$75K. An enterprise ERM design engagement at a mid-cap firm typically lands $150K-$500K depending on entity count.
Cyber risk assessments and penetration testing run $50K-$250K per scope. Annual GRC platform licenses range from $30K for mid-market specialists to $500K+ for enterprise suites.
Total program cost for a US mid-cap usually clears 0.3-0.7% of revenue once internal staff and external risk management services are combined.
Should we build internal capability or buy risk management services?
Hybrid is the right answer for most US firms. Build internal capability for daily operations — register maintenance, KRI monitoring, routine reporting — and buy specialized risk management services for periodic assessments, scarce skills (penetration testing, scenario modeling, M&A due diligence), and independent assurance.
The structure tracks the IIA Three Lines Model. Pure outsourcing rarely works because regulators expect embedded ownership; pure internal builds rarely work because the skill gap is too wide.
Which frameworks should risk management services align to?
US risk management services should align to ISO 31000:2018 for risk management principles, COSO ERM for governance integration, NIST CSF 2.0 for cybersecurity, ISO 27001:2022 for information security, and ISO 22301 for business continuity.
Public issuers add SEC cybersecurity disclosure-rule artifacts; banks add OCC heightened standards. Avoid providers who use only proprietary methodology — that creates vendor lock-in and weak audit trail.
How are risk management services different from internal audit?
Risk management services and internal audit are complementary, not substitutes. Internal audit (third line) provides independent assurance that controls are designed and operating effectively.
Risk management services (first or second line) help build, calibrate, and operate the risk program itself. Internal audit tests the program; risk management services help design the program being tested.
Confusing the two erodes independence and weakens both functions. The IIA’s 2020 update to the Three Lines Model formalized the boundary.
How do risk management services support board and audit committee reporting?
Mature risk management services produce three artifacts the board can act on: a risk heat map showing residual risks against appetite, a top-10 risk register with owners and remediation status, and a KRI dashboard with trend data.
The audit committee wants signal change, not point-in-time snapshots. Programs that report breach history and remediation closure next to each risk score consistently get faster approvals on resource asks. For format guidance, see how to use a key risk indicators dashboard.
How long do risk management services engagements usually take?
A targeted compliance gap analysis runs four to eight weeks. An ERM framework design engagement runs three to six months.
A full enterprise GRC platform implementation runs nine to eighteen months. Cyber risk assessments run two to six weeks per scope.
Strategic risk advisory engagements often run as quarterly retainers rather than projects. Phased rollouts beat big-bang in almost every case — start with one risk domain, prove the workflow, then expand to adjacent ones.
What are the biggest 2026 trends shaping risk management services?
AI-augmented risk identification, third-party risk consolidation, real-time risk telemetry, and the regulatory push toward continuous compliance are the four trends reshaping risk management services through 2027.
The EU AI Act obligations going active in August 2026 and the SEC cybersecurity disclosure rule are the regulatory anchors. Programs that pair their risk management services with quarterly recalibration and live KRI dashboards will be the ones that hold up under regulatory and customer-audit scrutiny.
Looking Ahead: Risk Management Services Through 2026 and 2027
Generative AI inside the GRC platform is reshaping risk management services faster than most buyers expected. AuditBoard, MetricStream, and ServiceNow GRC all shipped AI-assisted assessment drafting and natural-language audit-evidence querying through 2025.
The NIST AI Risk Management Framework supplies the methodology layer; the EU AI Act sets the deadline. Programs that build governance for the AI sitting inside their own platform will move ahead of the ones still treating AI as a vendor problem.
Third-party risk is consolidating into the wider program rather than running on its own. The Verizon 2025 DBIR found third-party involvement in breaches doubled to 30%, which is enough to force the integration.
Newer TPRM programs now monitor 275+ third parties. At that count, annual reassessments stop being credible and continuous monitoring becomes the only workable answer — for cost as much as for risk.
Compliance is going continuous, with regulators leading the change. The SEC cybersecurity disclosure rule pushed material-incident reporting onto a four-business-day cycle, and state privacy laws are tracking the same direction. Annual risk assessments cannot meet that cadence. Risk management services that wire continuous monitoring into the assessment lifecycle and recalibrate KRIs quarterly will hold up under SEC, FTC, and customer-audit scrutiny in 2027.
Operationalize Your Risk Management Services Program
At riskpublishing.com we help US organizations design and operate risk management services across the six service lines covered above.
Engagements usually include a maturity assessment against ISO 31000 and COSO ERM, a risk-appetite workshop, a 12-month implementation roadmap, KRI dashboard design, and a quarterly board-paper template. We work alongside internal teams rather than replacing them — the IIA Three Lines Model already explains why.
Explore our risk advisory services, or contact us to scope a risk management services engagement tailored to your industry, regulatory footprint, and 2026-2027 priorities.
Related reading on riskpublishing.com — for buyers scoping their next engagement: enterprise risk management framework, operational risk management framework, compliance risk assessment framework, supply chain key risk indicators, risk management lifecycle, risk appetite statements examples, guide to information security risk management, and the integrated risk management approach. Each one walks through a specific service line in more depth than this overview can carry.

Chris Ekai is a Risk Management expert with over 10 years of experience in the field. He has a Master’s(MSc) degree in Risk Management from University of Portsmouth and is a CPA and Finance professional. He currently works as a Content Manager at Risk Publishing, writing about Enterprise Risk Management, Business Continuity Management and Project Management.
