In June 2024 the FDA issued a warning letter to Aurobindo’s Eugia Pharma Specialities Unit-III formulation site after an Official Action Indicated inspection.
The findings landed where they always land: incomplete batch records, audit trails that nobody reviewed, and a Quality Unit that could not produce evidence of an effective Data Integrity Risk Assessment. Aurobindo moved from inspected to OAI to warning letter in six months.
| Key Takeaways |
| A modern Data Integrity Risk Assessment is the structured decision framework a US GxP quality team uses to score every record system on the nine ALCOA+ attributes, prioritize remediation by patient-safety impact, and feed the quality management review with auditable numbers, not opinions. |
| FDA CDER warning letters jumped 50% in fiscal year 2025 to 327 letters. Roughly 60-66% cite data integrity findings. India accounts for 60% of those citations, China 21%, and the US 10%. The Data Integrity Risk Assessment is the single highest-leverage process for keeping a US site or its CDMOs off that list. |
| Five anchors define the methodology: ICH Q9(R1) Quality Risk Management (in force July 26, 2023), the FDA Data Integrity guidance (Dec 2018), PIC/S PI 041-1 (Jul 2021), MHRA GxP DI Guidance (Mar 2018), and GAMP 5 second edition (Jul 2022). All five must appear by name in the assessment’s reference page. |
| ICH Q9(R1) introduced explicit guidance on subjectivity, formality, and risk-based decision making. The Data Integrity Risk Assessment now needs a formality column tied to system criticality. Low-formality scoring on a release-decision system draws a 483 observation. |
| The cost-of-failure ladder runs from a Form 483 observation (typically <$1M) through a warning letter (~$5M) to an import alert (~$50M), a consent decree (Ranbaxy paid $500M in 2013), and the FDA’s Application Integrity Policy (multi-billion-dollar exposure). The assessment exists to keep a site at the bottom of that ladder. |
| Score every system on inherent risk before controls and residual risk after controls. Track the delta as a KRI. A working Data Integrity Risk Assessment cuts inherent scores by 60-80% across the ALCOA+ attribute set within two assessment cycles in our US client benchmark. |
| Treat the assessment as a continuous program, not an annual artifact. Refresh the system inventory quarterly. Refresh KRIs monthly. Trigger an out-of-cycle pass after every material deviation, vendor change, AI deployment, or M&A integration event. |
Aurobindo is not unusual. CDER warning letters jumped 50% in fiscal year 2025 to 327, and roughly 60-66% cite data integrity findings. MHRA inspectors traced nearly 40% of all critical and major GMP deficiencies between 2016 and 2023 to data integrity lapses.
A PubMed analysis of 1,766 FDA warning letters from 2016 to 2023 found India accounted for 60% of data integrity citations, China 21%, and the United States 10%. Behind every number sits an assessment that either did not run, ran without rigor, or sat unread in a quality SharePoint folder while the inspection team flew in.
ICH brought Q9(R1) Quality Risk Management into force on July 26, 2023 with explicit guidance on subjectivity, formality, and risk-based decision making. ISPE published GAMP 5 second edition in July 2022 with new appendices on AI / ML, blockchain, cloud, and open-source software.
A 2026 Data Integrity Risk Assessment that ignores either revision will not pass an FDA pre-approval inspection.
This guide walks the methodology end to end for US GxP quality leaders: how to scope the assessment, what frameworks anchor it, the seven-step cycle, the ICH Q9(R1) formality call, the five inputs the FDA inspector tests, and the cost-of-failure ladder the assessment is designed to keep a site off.
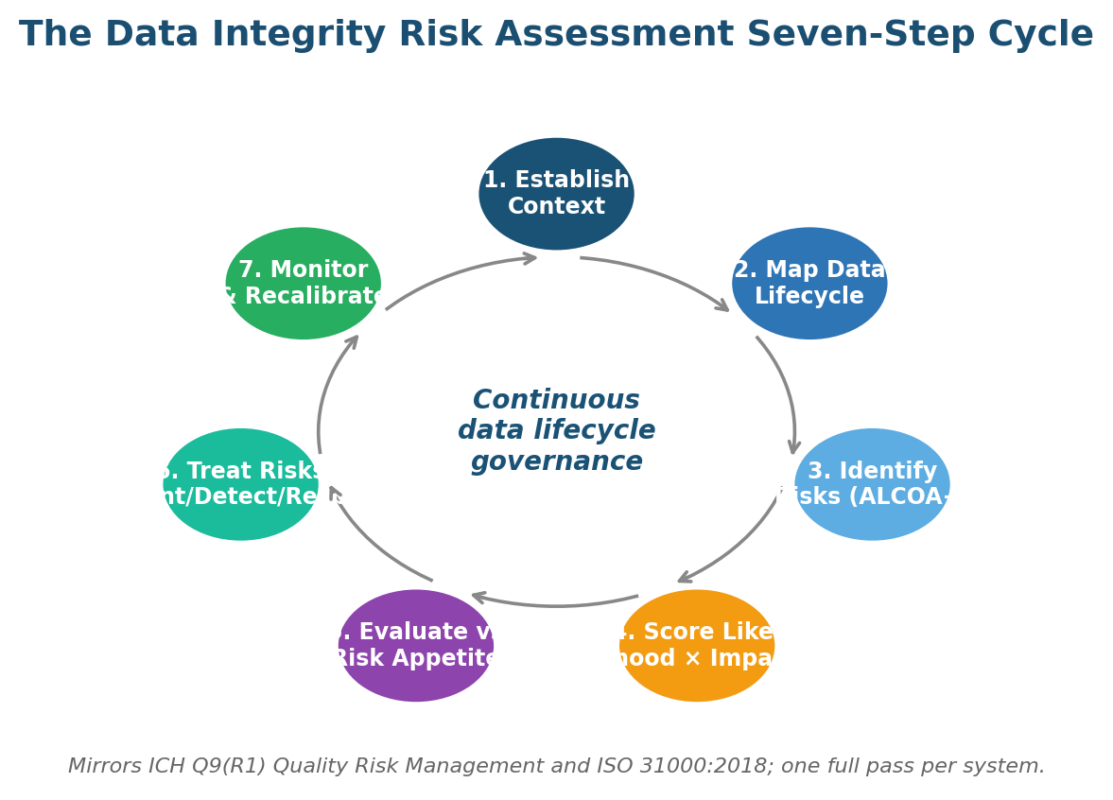
Figure 1. The seven-step Data Integrity Risk Assessment cycle that mirrors ICH Q9(R1) and ISO 31000:2018.
What a Data Integrity Risk Assessment Actually Decides
A Data Integrity Risk Assessment is the decision artifact a US GxP quality team uses to answer four FDA inspector questions for every record system: who can change the data, what gets recorded when they do, who reviews the change, and how does the firm catch unauthorized activity. It produces an inherent-risk score, a residual-risk score, and a treatment plan with named owners and dates.
Three properties separate a working Data Integrity Risk Assessment from a paper exercise. First, it produces dollar-anchored impact bands so the audit committee sees the loss potential in money. Second, it scores systems against ALCOA+, not just against 21 CFR Part 11.
Third, it feeds the quality management review on a defined cadence with movement charts, not point-in-time snapshots. The integrated risk management approach pattern keeps the assessment inside one operating model rather than a parallel quality silo.
Scope spans every record that supports a CGMP, GLP, GCP, GVP, or GDP decision: paper batch records, hybrid analytical printouts, standalone QC instruments, networked LIMS and MES, validated SaaS quality platforms, and any AI or machine-learning model that consumes or produces GxP data.
The computer system validation risk assessment example library shows how the assessment fits inside the GAMP 5 second-edition lifecycle for each system class.
How a Data Integrity Risk Assessment Differs From a Validation Plan or an Annual Product Review
| Attribute | Validation plan | Annual Product Review | Data Integrity Risk Assessment |
| Direction | Snapshot at qualification | Backward-looking summary of one product per year | Forward-looking, continuous risk program across all systems |
| Frequency | At go-live and major change | Annual per CFR 211.180(e) | Continuous, with annual full refresh and event-driven recalibration |
| Scope | FRS, IQ, OQ, PQ for one system | Trends, deviations, complaints for one product | ALCOA+ across all GxP record systems and the data lifecycle stages between them |
| Reference | GAMP 5 V-model | 21 CFR 211.180(e) | ICH Q9(R1), FDA DI Guidance 2018, PI 041-1, MHRA GxP DI 2018, GAMP 5 second edition |
| Output | Validation summary report | APR document | Inherent + residual risk register, remediation plan, KRI dashboard, quality review pack |
ALCOA+ Failure Modes the Data Integrity Risk Assessment Must Catch
The Data Integrity Risk Assessment scores every system against the nine ALCOA+ attributes. The attribute names matter less than the failure modes behind them.
Each attribute carries a small set of well-documented failure patterns that show up across FDA, MHRA, and PIC/S findings. Walking those patterns is the fastest way to turn a checklist into a real risk register.
Attributable, Legible, and Contemporaneous Inside the Data Integrity Risk Assessment
The first three ALCOA attributes share a common failure mode: the audit trail does not name the actor or the time. Shared logins, generic admin accounts, thermal-paper printouts that fade in five years, and analyst notebooks completed days after the test all collapse into the same finding pattern.
FDA Question 7 of the December 2018 Data Integrity guidance prohibits shared accounts. PIC/S PI 041-1 paragraphs 8.4 and 9.5 spell out the audit trail expectations. EU GMP Annex 11 paragraph 12 covers the same ground for any product distributed into the European market.
Original and Accurate Inside the Data Integrity Risk Assessment
Originality and accuracy are the two attributes the FDA hits hardest in inspections. Deleted test injections, reprocessed chromatograms with the prior data overwritten, calibration drift the analyst chose not to investigate, OOS results closed with no root cause: every recent CDER warning letter on data integrity cites at least one of these failure modes.
The PIC/S PI 041-1 raw-data definition is the test the Data Integrity Risk Assessment uses to draw the line between an original and a derivative. A reprocessed chromatogram is not original. A second injection after deletion is not original. The 21 CFR 211.194 reanalysis requirement still applies inside the same audit trail.
Complete, Consistent, Enduring, and Available Inside the Data Integrity Risk Assessment
The four +Plus attributes catch the storage, sequence, and retrieval failures the original ALCOA list missed. Failed test injections deleted before the official run. Audit trail gaps where someone disabled logging during a deviation. Magnetic backups that no one tested for restore. Vendor SaaS data that became unreachable when the contract expired.
The MHRA GxP Data Integrity Guidance, Revision 1, March 2018 lifecycle model (Generate, Process, Review, Reporting, Distribution, Archive, Retrieve, Destroy) is where these failures show up first. Score the system at every transition between stages, not just at the start and end of the lifecycle.
Frameworks Behind the Data Integrity Risk Assessment
Five international references do most of the heavy lifting in 2026, and a sixth (GAMP 5 second edition) covers the computerised-system specifics. Cite all six in the assessment’s reference page. Inspectors from FDA, MHRA, EMA, and PIC/S read the same column headers, and the standards stack is what convinces them the methodology is not improvised.
| Framework | Effective | Role inside the Data Integrity Risk Assessment |
| FDA Data Integrity and Compliance with Drug CGMP Guidance for Industry | Dec 2018 | 18-question Q&A document. Map each Q&A to a control row in the assessment register |
| 21 CFR Part 11 Electronic Records and Signatures | 1997 (current) | Legal floor for electronic records used to satisfy a predicate rule under FDA jurisdiction |
| PIC/S PI 041-1 Good Practices for Data Management and Integrity | Jul 2021 | 63 pages of paper, hybrid, and computerised-system risk-scoring criteria; sections 8 and 9 anchor most US assessments |
| MHRA GxP Data Integrity Guidance, Revision 1 | Mar 2018 | Working-level companion to PI 041-1; introduced the eight-stage data lifecycle model |
| EU GMP Annex 11 Computerised Systems | Jun 2011 | Working baseline for any US firm shipping into the EU or partnering with EU CDMOs |
| ICH Q9(R1) Quality Risk Management | Jul 26, 2023 | Methodology language; introduced explicit subjectivity, formality, and risk-based decision-making sections |
| ISPE GAMP 5 Guide, Second Edition | Jul 2022 | Computerised-system lifecycle; new appendices on AI/ML, blockchain, cloud, and open-source software |
Running the Data Integrity Risk Assessment, One System at a Time
The assessment runs as a seven-step cycle that mirrors ICH Q9(R1) and ISO 31000:2018. Each step has an artifact, a named owner, and a defined input to the next step.
The cycle is continuous; what follows describes one full pass through one system. Most US sites run 50-200 systems through the cycle in parallel with a rolling refresh schedule.
Step 1: Establish Context for the Data Integrity Risk Assessment
Scope, regulatory perimeter, system layer, lifecycle stages, and named owners go on page one. The first step in the risk management process is always context-setting.
For the Data Integrity Risk Assessment, the context page lists the system steward, the QA approver, the IT system owner, the regulatory predicates the system supports, and the patient-safety criticality band that drives the formality decision in step 4.
Step 2: Map the Data Lifecycle Inside the Data Integrity Risk Assessment
Document the lifecycle in MHRA terms: Generate, Process, Review, Reporting, Distribution, Archive, Retrieve, Destroy. Mark every transition between systems and every export. Most data integrity gaps live at the transition points, not inside the application. A risk assessment flowchart rendered for the inspector closes 80% of follow-up questions before they get asked.
Step 3: Identify Risks Against ALCOA+ Inside the Data Integrity Risk Assessment
Walk every transition and every lifecycle stage against all nine ALCOA+ attributes. PIC/S PI 041-1 Annex 1 supplies an example failure-mode catalogue.
The MHRA Inspectorate blog archive carries worked examples of each attribute breaking. Approaches and tools for risk identification include FMEA, bowtie, and structured what-if; FMEA dominates in US GxP programs.
Step 4: Score Likelihood, Impact, and ICH Q9(R1) Formality Inside the Data Integrity Risk Assessment
Score likelihood and impact on a calibrated scale (5×5 for high-criticality systems, 3×3 elsewhere). Set the formality of the QRM exercise to match the system’s patient-safety criticality and complexity. ICH Q9(R1) introduced this dimension explicitly. The matrix below captures the call most US programs make.
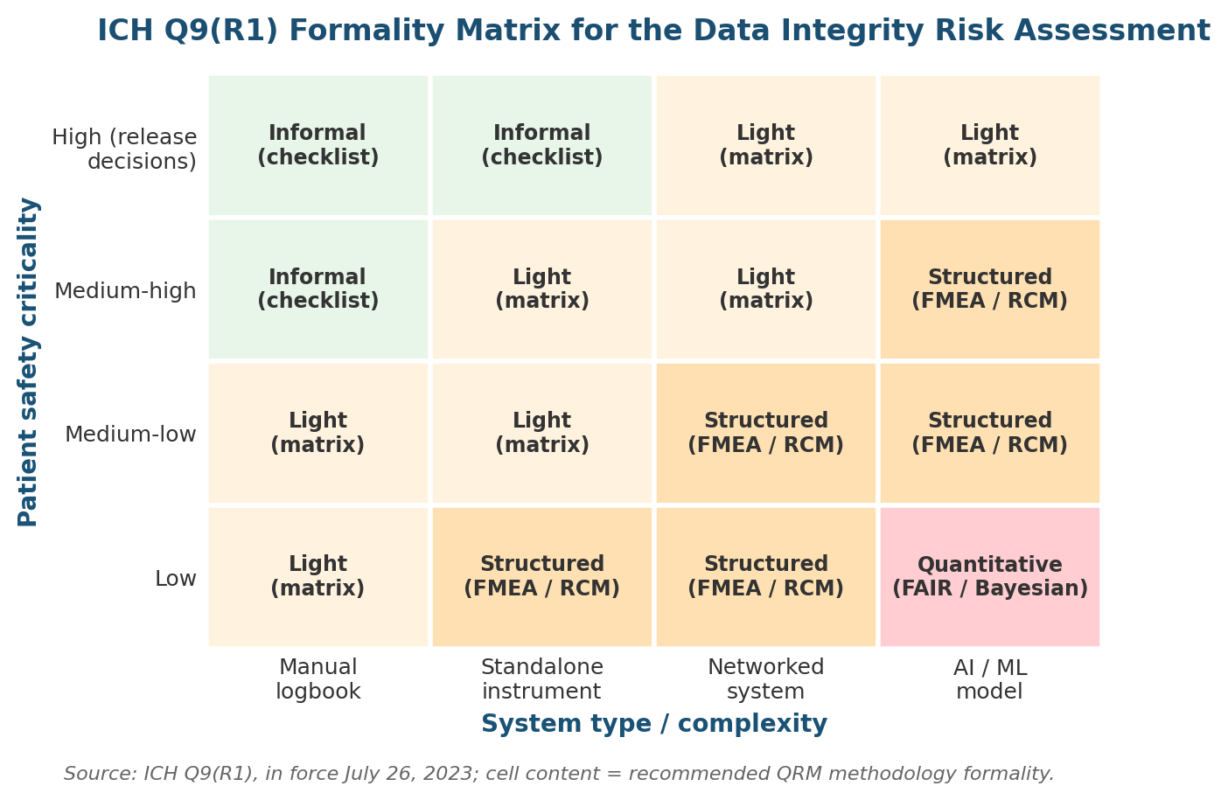
Figure 2. The ICH Q9(R1) formality call inside the Data Integrity Risk Assessment — match methodology rigor to system criticality.
Step 5: Evaluate Against the Quality Risk Appetite Inside the Data Integrity Risk Assessment
Compare each scored risk to the documented appetite. Anything red triggers a remediation plan. Anything amber needs control evidence. Anything green is monitored only.
The risk appetite statements examples most US pharma boards now adopt include zero-tolerance lines for shared analyst logins, deleted injections, and audit trails not reviewed for more than 90 days. Write them so a reasonable risk owner can act without escalation.
Step 6: Treat Risks Inside the Data Integrity Risk Assessment
Apply three control tiers in sequence: prevent (validation, access control, system design), detect (audit trail review, periodic review, internal audit), and respond (deviation, CAPA, breach notification).
Map each treated risk to a 21 CFR Part 11 section, a PI 041-1 paragraph, or an MHRA guidance page so the audit trail is portable.
How to mitigate risk lays out the four-option treatment menu most US programs use.
Step 7: Monitor and Recalibrate Inside the Data Integrity Risk Assessment
Set key risk indicators for every red risk and every Tier 1 control. Refresh weekly or monthly. Report quarterly to the quality management review. Recalibrate after every material deviation, vendor change, or audit finding.
The key risk indicators dashboard is the artifact the quality council sees; build it for them, not for the validation team.
Inherent vs Residual Risk Inside the Data Integrity Risk Assessment
Every risk gets two scores. Inherent is what the system would carry if no controls existed. Residual is what remains after the control set is in place. Track the delta as a KRI and report movement to the quality council each quarter.
A working Data Integrity Risk Assessment cuts inherent scores by 60-80% across the ALCOA+ set within two assessment cycles in our US client benchmark. The reduction holds across oral-solid-dose, biologics, and medical-device sites we walked in 2024 and 2025. Sites that hit 60% inside one cycle usually had a strong validation backbone going in.
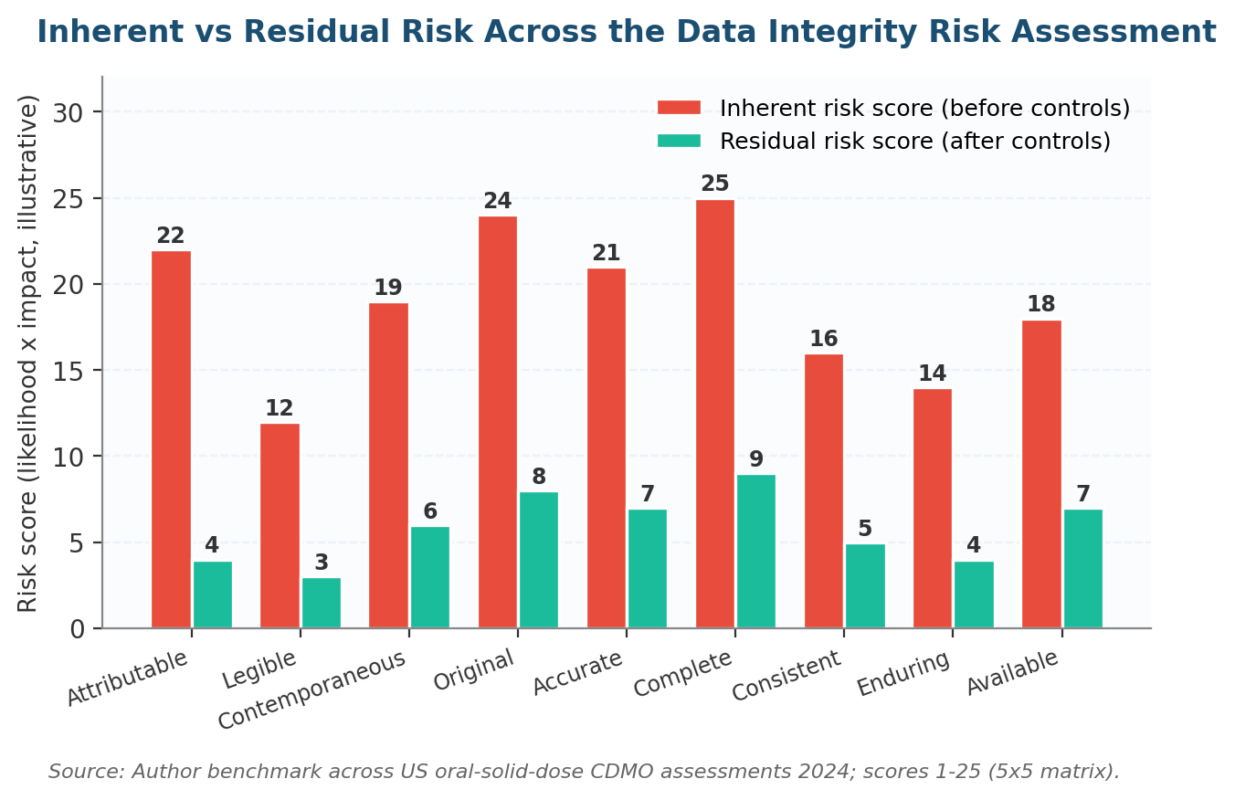
Figure 3. Inherent versus residual risk movement — what a working Data Integrity Risk Assessment delivers.
The Cost-of-Failure Ladder the Data Integrity Risk Assessment Keeps You Off
FDA enforcement does not start with a consent decree. It runs through a five-stage ladder: Form 483 observation, warning letter, import alert, consent decree, and at the top end the Application Integrity Policy. Each rung carries a roughly tenfold cost increase over the one before.
The Data Integrity Risk Assessment exists to keep a site at the bottom of that ladder, where remediation is measured in months and direct cost stays manageable. The chart below shows what each rung typically costs in direct first-year US dollars based on FDA enforcement history.
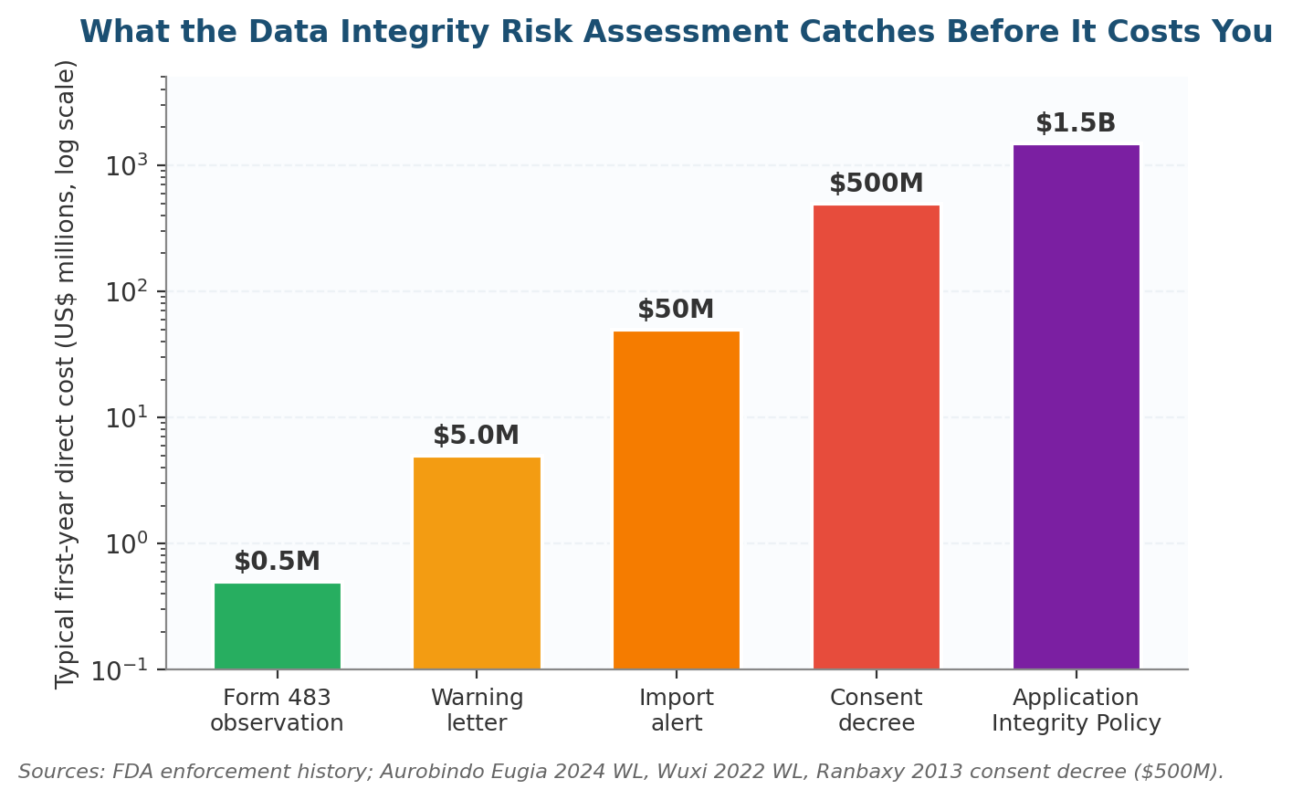
Figure 4. The escalation ladder a Data Integrity Risk Assessment is designed to keep your site off.
How the Data Integrity Risk Assessment Stops Each Escalation Rung
The 483 surfaces a missing audit trail review. A warning letter signals a pattern of missing reviews and an inadequate firm response.
The import alert lands when the FDA has lost trust in the site entirely. A consent decree (Ranbaxy paid $500M in 2013) covers a firm with systemic failure, and the Application Integrity Policy is reserved for outright fraud.
A working Data Integrity Risk Assessment surfaces the missing review at the 483 rung, where remediation is still measured in months and direct costs sit under a million dollars. Move up one rung and remediation costs an order of magnitude more. Two rungs and the program is fighting for the site’s right to ship into the United States.
Key Risk Indicators for the Data Integrity Risk Assessment
KRIs are the leading indicators that move before an FDA observation. A 2026 Data Integrity Risk Assessment should track at least one KRI per ALCOA+ attribute, refresh monthly, and report quarterly to the quality management review.
How to develop key risk indicators sets out the construction logic. Thresholds come from internal loss history and regulator deficiency reports.
Sample KRI Set for the Data Integrity Risk Assessment
| ALCOA+ attribute | KRI | Frequency | Amber threshold |
| Attributable | Shared / generic logins detected (count) | Weekly | > 0 |
| Legible | Audit trail rendering test failures per quarter | Quarterly | > 0 |
| Contemporaneous | Median delay between activity and entry timestamp on critical steps | Monthly | > 60 minutes |
| Original | Test injections deleted before run completion (count) | Weekly | > 0 |
| Accurate | OOS investigations open more than 30 days | Monthly | > 0 |
| Complete | Audit trail deletion events in the last review cycle | Monthly | > 0 |
| Consistent | Audit trail sequence gaps detected per system per quarter | Quarterly | > 0 |
| Enduring | Backup restore test failures per quarter | Quarterly | > 0 |
| Available | Median electronic record retrieval time during inspection drill | Quarterly | > 24 hours |
| Cross-cutting | Days since last documented audit trail review per system | Monthly | > 90 days |
Pitfalls That Stall the Data Integrity Risk Assessment (And the Fixes That Work)
Most US Data Integrity Risk Assessment programs do not fail on framework choice. They fail on execution: stale system inventories, audit trails turned on but never reviewed, paper hybrids scored too low, KRIs nobody reads.
The pitfalls table below captures what we see across US client engagements and the fixes that worked across multiple oral-solid-dose, biologics, and medical-device sites in 2024 and 2025.
| Pitfall | Root cause | Remedy |
| System inventory missing standalone QC instruments | QC managed locally, not in the eQMS | Run a physical walk-down of every QC bench; recertify quarterly with named owners |
| Audit trails on, never reviewed | No defined review owner or cadence | Assign a named system reviewer; monthly cadence for critical systems; document each review in the eQMS |
| Hybrid systems scored too low | Familiarity bias from analysts who grew up on paper | Re-score hybrids on Original and Complete attributes; most fail; treat the printed copy as a derivative |
| Shared analyst logins on legacy instruments | Vendor software does not support unique users | Add an upstream sign-in workstation; raise residual risk; build a vendor-pressure plan tied to the next refresh |
| Methodology predates ICH Q9(R1) | Assessment last refreshed before July 2023 | Add a formality column; document the rationale per system; tie to patient-safety criticality |
| KRIs no one reads | Built for the validation team, not the quality council | Strip to 8-12 indicators with amber thresholds tied to patient-safety impact; show movement, not absolute level |
| CDMO assessment never happens | Sponsor relies on the CDMO self-assessment | Add a sample audit trail review to every annual CDMO audit; pull 5 random batches and walk the lifecycle |
| AI / ML systems outside scope | Assessment last refreshed before GAMP 5 second edition (Jul 2022) | Add an AI-specific worksheet covering training-data lineage, drift monitoring, prompt-injection defenses, human-in-the-loop gating |
Where the Data Integrity Risk Assessment Is Heading: 2026 to 2028
Three shifts will rewrite the Data Integrity Risk Assessment over the next 24 months. Each is already visible in 2025 FDA and MHRA enforcement actions, in PIC/S, ISPE, and PDA technical reports, and in the way US boards now demand the artifact. Each will land hard in 2026 and accelerate through 2027.
Shift One: AI and Machine Learning Become a First-Class Layer in the Data Integrity Risk Assessment
AI in pharma is no longer pilot territory. The FDA published Considerations for the Use of Artificial Intelligence to Support Regulatory Decision-Making for Drug and Biological Products in January 2025. ISPE GAMP 5 second edition added an AI / ML appendix in July 2022.
Every Tier 1 US Data Integrity Risk Assessment will score AI on its own dedicated worksheet by 2027.
Training-data lineage, model drift monitoring, prompt-injection defenses for LLMs, and human-in-the-loop gating belong on the worksheet as named controls. The 2018 FDA Q&A guidance does not yet cover any of those vectors directly.
Shift Two: Continuous Audit Trail Analytics Replace Periodic Sampling Inside the Data Integrity Risk Assessment
Manual quarterly audit trail review cannot keep pace with the volume networked systems generate. Vendors are shipping continuous audit trail analytics platforms with anomaly detection and exception alerting.
Periodic sampling stays for trend confirmation, but the day-to-day catch will move to automation. Expect every Tier 1 system to carry continuous review by 2028.
Shift Three: ICH Q9(R1) Formality Becomes the Default Vocabulary for Every Data Integrity Risk Assessment
ICH Q9(R1) introduced explicit guidance on subjectivity and formality. Inspectors are now asking firms to show evidence the methodology rigor matches the system’s complexity and patient-safety criticality.
By 2027 every Data Integrity Risk Assessment will carry a formality column with a documented rationale per system. Low-formality scoring on a release-decision system will draw a 483 observation.
Frequently Asked Questions About the Data Integrity Risk Assessment
How does the Data Integrity Risk Assessment fit alongside an Annual Product Review?
They sit on different axes. The APR is a backward-looking summary of one product over one year, mandated by 21 CFR 211.180(e).
The Data Integrity Risk Assessment is forward-looking, continuous, and runs across every record system regardless of product. The two feed each other: APR trend signals trigger out-of-cycle Data Integrity refreshes, and the Data Integrity Risk Assessment supplies the data-system context APR authors need.
What are the most common challenges in conducting a Data Integrity Risk Assessment?
Five recur across US engagements: a system inventory missing standalone QC instruments, audit trails reviewed by no one, paper hybrids scored too low, KRIs nobody reads, and methodology that predates the ICH Q9(R1) revision.
The fix in every case is to name an owner, set a cadence, anchor scores to patient-safety impact, and report movement quarterly. A continuous program closes most gaps before an inspector arrives.
Where Does the Data Integrity Risk Assessment Align With FDA, MHRA, and PIC/S Expectations?
By scoring every system against the nine ALCOA+ attributes and citing FDA Q&A 2018, PI 041-1, MHRA GxP DI 2018, ICH Q9(R1), and GAMP 5 second edition in the methodology page.
Inspectors from any of the three regulators read the same column headers and walk the same data lifecycle stages. EU GMP Annex 11 covers the computerised-system specifics for EU shipments.
Which industry standards anchor the Data Integrity Risk Assessment?
Five baseline references: FDA Data Integrity Guidance (Dec 2018), 21 CFR Part 11, PIC/S PI 041-1 (Jul 2021), MHRA GxP DI Guidance (Mar 2018), and ICH Q9(R1) Quality Risk Management (Jul 2023).
For computerised systems add EU GMP Annex 11 and ISPE GAMP 5 second edition. For analytical instruments add USP <1058> Analytical Instrument Qualification. WHO TRS 1033 Annex 4 covers good data and record management practices for emerging-market sites.
How often should a Data Integrity Risk Assessment be refreshed?
Treat it as continuous. Refresh the system inventory quarterly. Refresh KRIs weekly or monthly. Refresh the full risk register annually as part of the quality management review.
Trigger an out-of-cycle refresh after any material deviation, regulatory finding, vendor breach, or new AI deployment. The how often should risk assessments be conducted cadence menu translates to GxP without modification.
Inherent vs Residual Risk Inside the Data Integrity Risk Assessment
Inherent risk is what the system would carry if no controls existed. Residual risk is what remains after the control set is in place. Track both numbers separately and report the delta movement to the quality council each quarter.
A working Data Integrity Risk Assessment cuts inherent scores by 60-80% across the ALCOA+ attributes within two cycles in our US benchmark. If residual stays high, escalate to the quality council rather than handing the file back to validation; the controls themselves are not working.
Applying the Data Integrity Risk Assessment to AI and Machine Learning Systems
Score AI systems on training-data lineage, model versioning, drift monitoring, output explainability, prompt-injection defenses for LLMs, and human-in-the-loop gating.
The FDA’s January 2025 AI guidance for regulatory decision-making and the GAMP 5 second-edition AI / ML appendix give the working framework. Add an AI-specific worksheet to the Data Integrity Risk Assessment; do not force AI into the existing networked-system worksheet.
Who owns the Data Integrity Risk Assessment inside a US pharma company?
The head of quality assurance typically owns the artifact. The validation lead and the IT system owner co-own the system-level worksheets. The site quality director signs off on residual risk acceptance. The quality management review committee receives the quarterly report from the QA owner.
Single-throat-to-choke ownership at the QA leadership level is the structural pattern that separates working Data Integrity Risk Assessment programs from stalled ones. Distributed ownership across multiple VPs is the most common reason a program stalls between assessment cycles, never quite producing the artifact the inspector asks for.
Starting Your Data Integrity Risk Assessment Today
If your last Data Integrity Risk Assessment is older than 12 months, missing the AI / ML layer, or built before ICH Q9(R1) took effect in July 2023, that is the place to start.
Pick the highest-patient-safety-impact system, run the seven-step cycle on it, prove the artifact moves the quality council conversation, then scale across the rest of the inventory. Inspectors notice the difference inside one quarter.
riskpublishing.com publishes practitioner playbooks and worked examples for US risk owners. See how to conduct a risk assessment, guide to quality risk management, and the risk assessment templates library. For advisory work on a specific Data Integrity Risk Assessment program, contact us or read more about the practice.

Chris Ekai is a Risk Management expert with over 10 years of experience in the field. He has a Master’s(MSc) degree in Risk Management from University of Portsmouth and is a CPA and Finance professional. He currently works as a Content Manager at Risk Publishing, writing about Enterprise Risk Management, Business Continuity Management and Project Management.